For both data security and information safety, it's common that most users have a liking for setting passwords on kinds of devices and specific folders to make them inaccessible to unauthorized users.
You may keep the passwords well by storing them in Apple Notes and TextEdit on Mac or managing them with a password manager. However, the trouble happens once you lost them accidentally.
No worries yet, this article from iBoysoft guides you to recover passwords with a professional toolkit - Passware. Let's get started then!
What is Passware?
Passware, also known as Password Kit, is a tool for decrypting files and quickly recovering passwords for more than three hundred file types including PDFs, ZIPs, and RARs. It has the capability to recover or reset passwords for Windows computers, macOS devices, and iPhones without a hitch.
On top of that, it is able to decrypt hundreds of applications including MS Office, QuickBooks, FileMaker, Lotus Notes, Bitcoin wallets, Apple Notes, Mac OS X Keychain, and password managers.
As the leading password software, Passware has a success rate of about 70%, which is quite good and easy to use. It has Basic, Standard, and Standard Plus kits are all intended for home use, although there are Business and even Forensics solutions available, depending on how difficult your job is.
How to use Passware to recover passwords?
This software prepares Predefined Settings based on the most frequently used password patterns, and each one targets different scenarios. You can have a look real quick here:
- Previous passwords: The recovered passwords are instantly added to the dictionary called "Previous Passwords" so that they can be tested on new files. The attack verifies various changes to the earlier passwords for additional files.
- Dictionary (short passwords): The attack checks the built-in English dictionary words up to 15 characters long with different case types. Dictionary Settings can be changed by double-clicking on the attack.
- Brute-force (short passwords): The attack checks all possible combinations of lowercase and uppercase letters, numbers, and symbols with an overall password length of up to 4 characters.
- Xieve (medium level): The attack checks passwords from 5 to 9 letters that look like English words, but are not necessarily dictionary words. Medium-level checks for less common combinations in lowercase.
- Brute-force (numbers): The attack checks numerical passwords from 5 to 8 characters.
- Joined attacks: The attack checks passwords that contain a dictionary word, followed by 1-2 numbers or symbols, and up to 4 numbers at the end.
- Joined dictionary: The attack checks passwords that contain two dictionary words with an overall password length of up to 9 characters.
- Brute-force (letters+numbers): The attack checks combinations of lowercase letters and numbers with an overall password length of 5 to 7 characters.
- Xieve (low level): The attack checks passwords from 5 to 9 letters that look like English words, but are not necessarily dictionary words. Low-level checks for the least common combinations.
According to the password you set, you can change the setting freely to recover it.
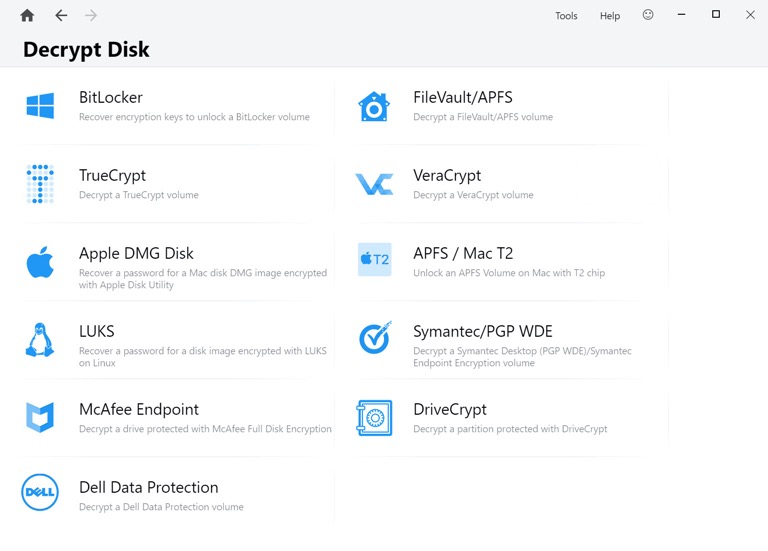
Moreover, Passware is able to decrypt BitLocker encrypted hard drives, Full Disk Encryption with FileVault2/APFS, and Apple DMG disk as well. Passware Kit scans the physical memory image file (acquired while the encrypted disk was mounted, even if the target computer was locked), extracts all the encryption keys, and decrypts the given volume.
The encryption keys might potentially be recovered from the hiberfil.sys file, which is automatically created when a system hibernates, if the target computer with the encrypted drive is shut off.
Conclusion
Passware Kit is such a professional and specially-designed toolset for people who lost passwords and have no access to locked devices or files and documents. It is able to decrypt the disk and make it possible to access data. If you're interested in it, try it now!
