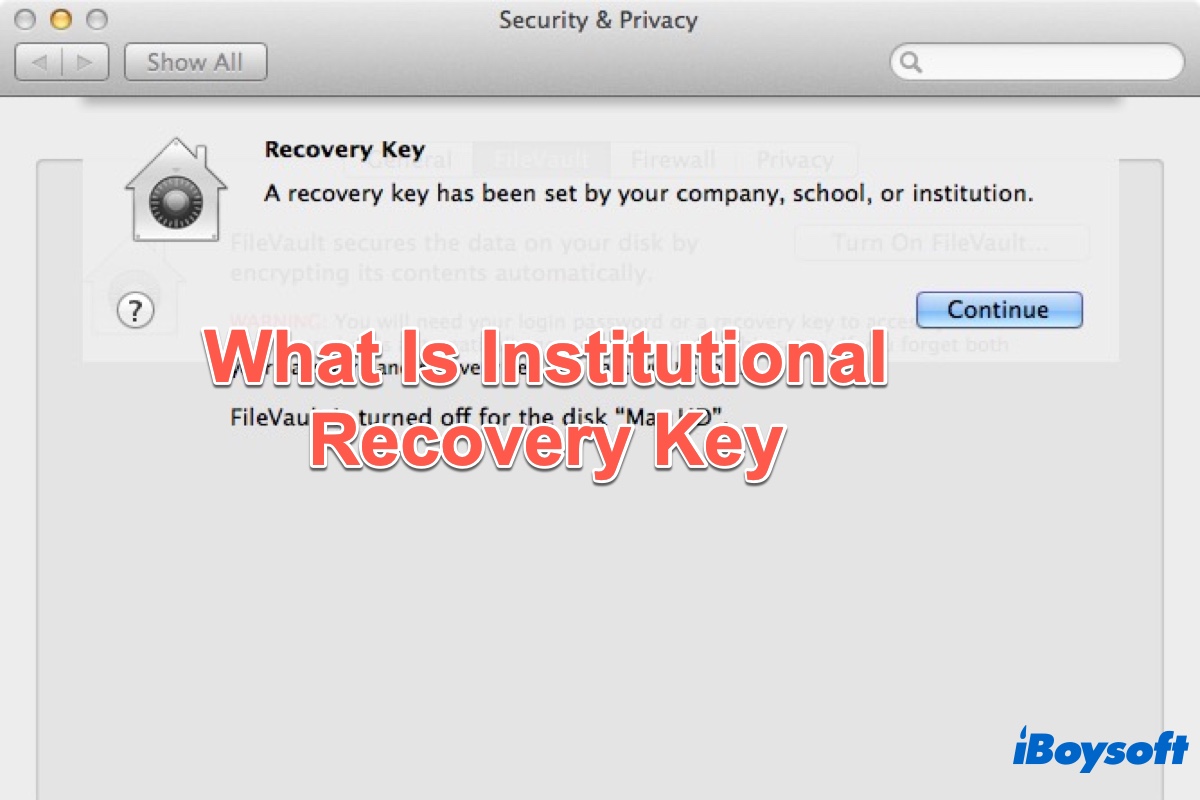
As a Mac user, you may have heard of Apple FileVault, a feature of Mac to securely protect your Mac. You may have used it to encrypt your Mac startup disk and get a recovery key. But do you know there is another key named the institutional recovery key(IRK) of FileVault?
If you have no idea, you can read this post to know the complete introduction to FileVault IRK. After you read this post, you will know what is institutional recovery key, and how to create, remove and use it.
What is the institutional recovery key
When FileVault 2 was announced initially, Apple stated that there would be two kinds of recovery keys available in it: PRK and IRK. A personal recovery key (PRK) is automatically generated at the time of encryption. Normally, it is an alphanumeric string and can be used to unlock your startup disk if you forget your FileVault password. We usually call it the FileVault recovery key.
An Institutional recovery key (IRK) is another thing. IRK is a pre-made recovery key that can be installed on a system prior to encryption and is most often used by a company, school, or institution to have one common recovery key that can unlock their managed encrypted systems. PRK itself can unlock a machine, but the institutional recovery key is used in combination with a password to unlock the keychain.
To have a deeper understanding of the institutional recovery key, just keep reading the next part to learn how to create/remove the FileVault IRK on Mac as well as how to use IRK to unlock Mac's startup disk.
Would you please share this post on your social media, thanks!
How to create a FileVault institutional recovery key
To create a FileVault institutional recovery key on your Mac or MacBook, just do the following:
- Go to Finder, open Applications > Utilities, and launch the Terminal app on your Mac,
- Enter the below command and press the Enter key:security create-filevaultmaster-keychain ~/Desktop/FileVaultMaster.keychain
- Enter the master password for the new keychain when asked, then enter it again when asked to retype.
- A key chain now is generated, and a file named FileVaultMaster.keychain is saved to your desktop. Copy this file to a secure location, such as an external hard drive. It is the private recovery key that can be used to unlock the startup disk of any Intel-based Mac set up to use the FileVault master keychain. It is not for distribution.
How to remove the IRK from the master keychain
If you need to remove FileVault IRK, follow these steps:
- Double-click the FileVaultMaster.keychain file on your desktop. The Keychain Access app will launch.
- From the Keychain Access sidebar, select FileVaultMaster.
- If the FileVaultMaster keychain is locked, choose File > Unlock Keychain "FileVaultMaster" from the menu bar, then enter the master password you created.
- From the two items shown on the right, select the one identified as "private key" in the Kind column.
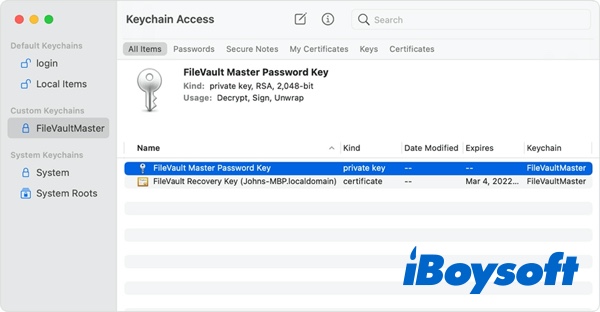
- Delete the private key: Choose Edit > Delete from the menu bar, enter the keychain master password, then click Delete when asked to confirm.
- Quit Keychain Access.
Now the FileVault master keychain on your desktop has been removed and should no longer contain the private key.
If you find this post helpful, please share it with more people!
How to use IRK to unlock a user's startup disk
To use the private key to unlock a user's startup disk, make sure you follow the below methods step by step:
- On the Mac or MacBook you want to unlock, start up the computer while holding the T key to boot into Mac Target Disk Mode. Release the T key once you see the Thunderbolt logo.
- Connect the Mac to another Mac (the host) using a Thunderbolt 3 (USB-C) cable. When you're asked to enter a password to unlock the disk, click Cancel.
- On the host Mac, connect the external drive that contains the private institutional recovery key.
If you stored the private recovery key in an encrypted disk image, double-click the file to mount the image and enter the password when prompted.
If you don't know the name of the startup volume (such as Macintosh HD) on the disk you want to unlock, open Disk Utility, then locate the volume name in the sidebar. You will need this information in the next step. - Open Terminal, then type in the following command to unlock the encrypted startup disk. Replace "name" with the name of the startup volume, and replace /path with the path to FileVaultMaster.keychain on the external drive or disk image:diskutil ap unlockVolume "name" -recoveryKeychain /pathHere's an example for a startup volume named Macintosh HD and a recovery-key volume named GDrive:diskutil ap unlockVolume "Macintosh HD" -recoveryKeychain /Volumes/GDrive/FileVaultMaster.keychain
- Input the master password to unlock the startup disk. If the password is accepted, the volume should mount on the Mac Desktop.
FAQs about FileVault institutional recovery key
- QWhat is the difference between institutional and personal recovery key?
-
A
First of all, the personal recovery key itself can unlock a machine, but the institutional recovery key is used in combination with a password to unlock the keychain. Secondly, most likely you're storing your personal recovery keys all in one place, it may be a secure place, but it's also a single breach point.
- QIs institutional recovery key the same as BitLocker key?
-
A
BitLocker recovery key (or Microsoft recovery key) is generated when a drive is encrypted using Microsoft BitLocker. The recovery key can be used to unlock/decrypt the encrypted drive if the user forgets or loses their password. The institutional recovery key is a pre-made recovery key with macOS FileVault and needs to unlock the encrypted drive together with a master password.