BitLocker, developed by Microsoft Windows, is a drive encryption feature that's used to address the threats of data theft or exposure. However, since 2015, this feature is abused by hackers to make it a new kind of virus to steal your data and extort money, known as BitLocker Virus.
This post will give a clear explanation of the BitLocker virus and show you how this fraud damages your drives. To access the drive again, one possible method is also offered. Read on to understand what BitLocker virus is.
An overview of BitLocker virus
Unlike general ransomware that runs in circulation, BitLocker virus is a new type of malware that exploits the Windows built-in feature, BitLocker. With BitLocker turned on, the entire disk, including all partitions, will be encrypted without adding extra encryption to a single partition or file.
Infected by BitLocker virus, this malware can create a BitLocker encrypted file that contains a virtual partition (VHD) and move all your data into this fake partition, known as VHD Locker Ransomware. What's worse, other than your Windows PC, all external hard drives, USB sticks, and other storage media can all encounter this ransomware.
In case you are wondering if would it be safe if the BitLocker encryption is turned off, the answer is no, unfortunately. Hackers can enable BitLocker functionality by executing simple commands. Then everything just falls into the same malware trap. Let's dive in to see how this scheme works in detail.
Now you know what is the BitLocker virus, why not share the info with more people?
How does BitLocker virus work
As mentioned above, the BitLocker virus will create an encrypted virtual partition and transfer all your data from the original location to it. Users that are hit by this ransomware are likely to encounter the following scenario in general.
First, when you try to access the partition that contains your precious data, you'll notice it's suddenly BitLocker encrypted and you have to enter the BitLocker password, which is only known to the hacker.
Next, your computer will reboot itself. Bad for you, this time the partition is not accessible at all.
Then, a Document note left by the hacker will show up on your Windows desktop with instructions telling you to pay the ransom in exchange for the BitLocker password. According to victims, the ransom can range from dozens to thousands in Bitcoin.
Obviously, it's not a wise choice to trust the hacker, but what about the data? How to unlock BitLocker drive without password & recovery key?
How to access data after BitLocker virus attack
Without the encryption password or the BitLocker recovery key, there's no way to access the data within the BitLocker-virus infected drive. Is it possible to have a clue about the password?
There are quite a few tricks malware uses to do evil. In BitLocker virus cases, the commonly used trick by hackers is one technique named With Password. Lucky for you, there's a way to guess the password if the hacker is using With Password to mess things up.
To verify which technique the hacker uses:
Step 1. Open Windows command prompt and choose Run as administrator.
Step 2. Type in the commands below and hit enter to check the method hackers use.
manage-bde -protectors
Please replace X with the drive letter of your victim drive.
Step 3. From the results above, you can see the used technique is the numerical password, which we can keep moving to find the password or the 48-digit key.
To find the BitLocker recovery key:
Step 1. Click on the Start button and type in Event Viewer. Click on the application to open it.
Step 2. On the left column, under Windows logs, click on System. On the right window, you can scroll up and down to find which partition is encrypted with BitLocker.
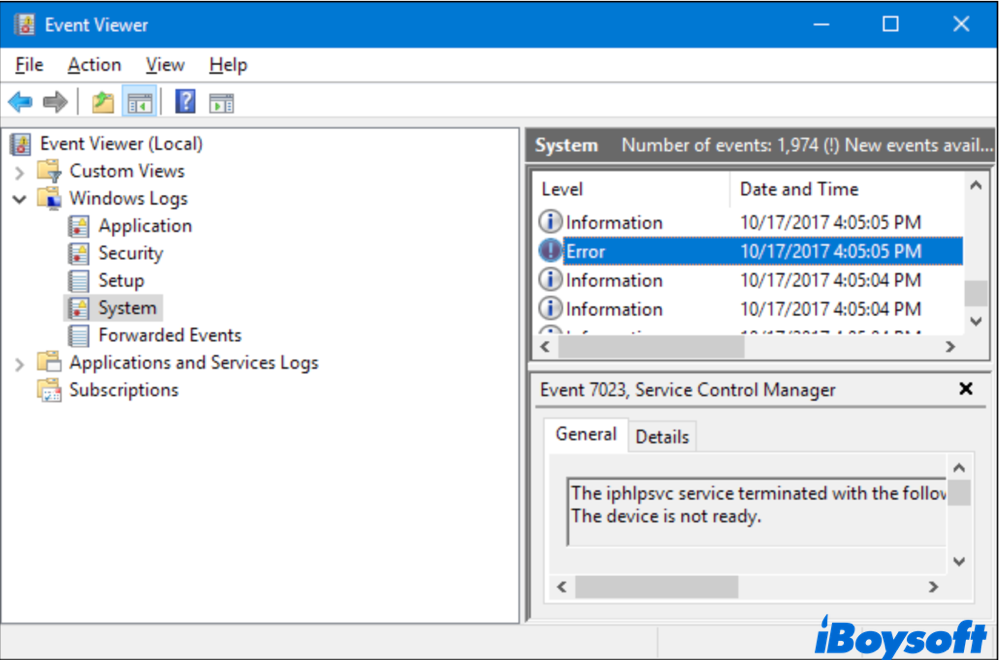
When the drive is BitLocker encrypted, a 48-digit .txt file will be created and saved. In this case, the .txt file must be saved locally on your PC since all these operations are done remotely by the hacker.
Step 3. In Windows Explorer, search for all .txt files created on the day your drive is hacked to be encrypted. Hopefully, you can find the right copy. However, it's also possible that the key is already deleted by the hacker.
If these steps help you out of trouble, why don't you share them to help others?
Conclusion
After reading this post, you should have a basic understanding of what is BitLocker virus and how it works the trick. Fortunately, there's still a chance that you can crack the password to access all your data.